What Happened?
Recently, threat actors have been seen abusing Microsoft Teams to launch phishing attacks.
While most Teams usage is intra-organizational, Microsoft enables external access by default. This allows members of one organization to add users outside the organization to their Teams chats.
This feature has provided malicious actors a new avenue by which to exploit untrained or unaware users. Researchers have observed a threat actor using this vector to send phishing lures delivering the DarkGate malware.
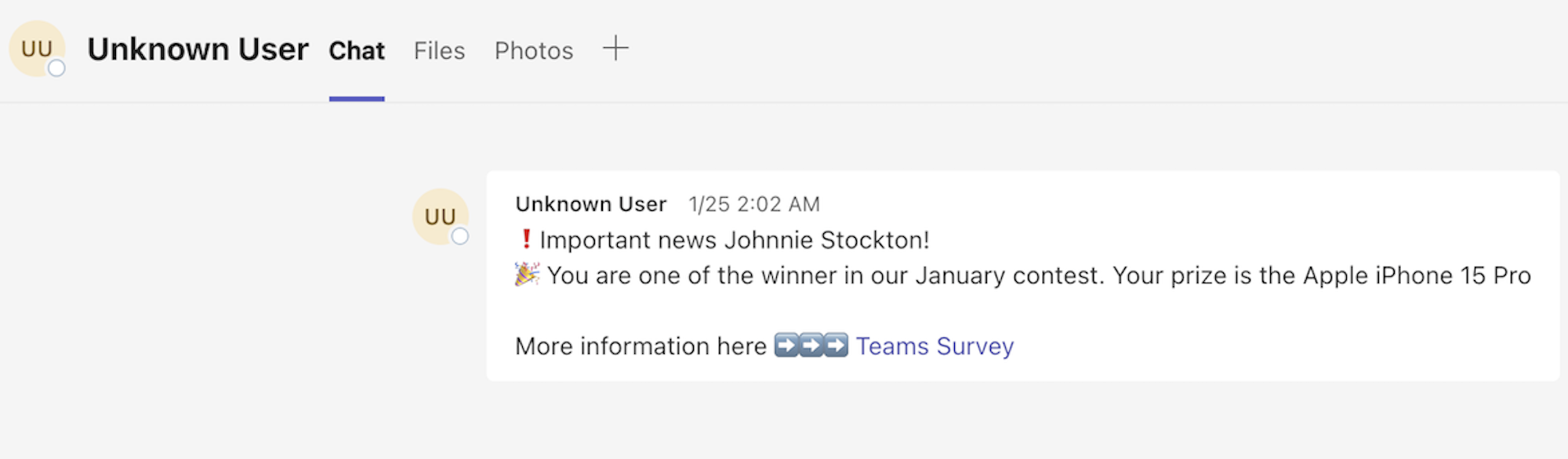
Below is an example of a Teams phishing message that was received by a Defender team member in a personal Teams account.
Defender Recommendations?
Unless absolutely necessary for daily business use, disabling external access in Microsoft Teams is advisable for Defender members. Email is generally a more secure and closely monitored communication channel.
If necessary, you can allow only specific external domains to an allow list. This will allow you to use Teams externally, if necessary (such as with clients).
The instructions for Microsoft Teams administrators to change organizational settings and user policies for external access can be found at the link below.
If you have any questions about Microsoft Teams external access, you can always reach out to Industry Defenders at memberservices@industrydefenders.com.
