On September 20th, the LockBit ransomware group announced that it had downloaded “all of the confidential data” of a payroll provider who provides worker’s compensation, 401k reporting, payroll and other services and who has offices in the midwestern part of the United States.
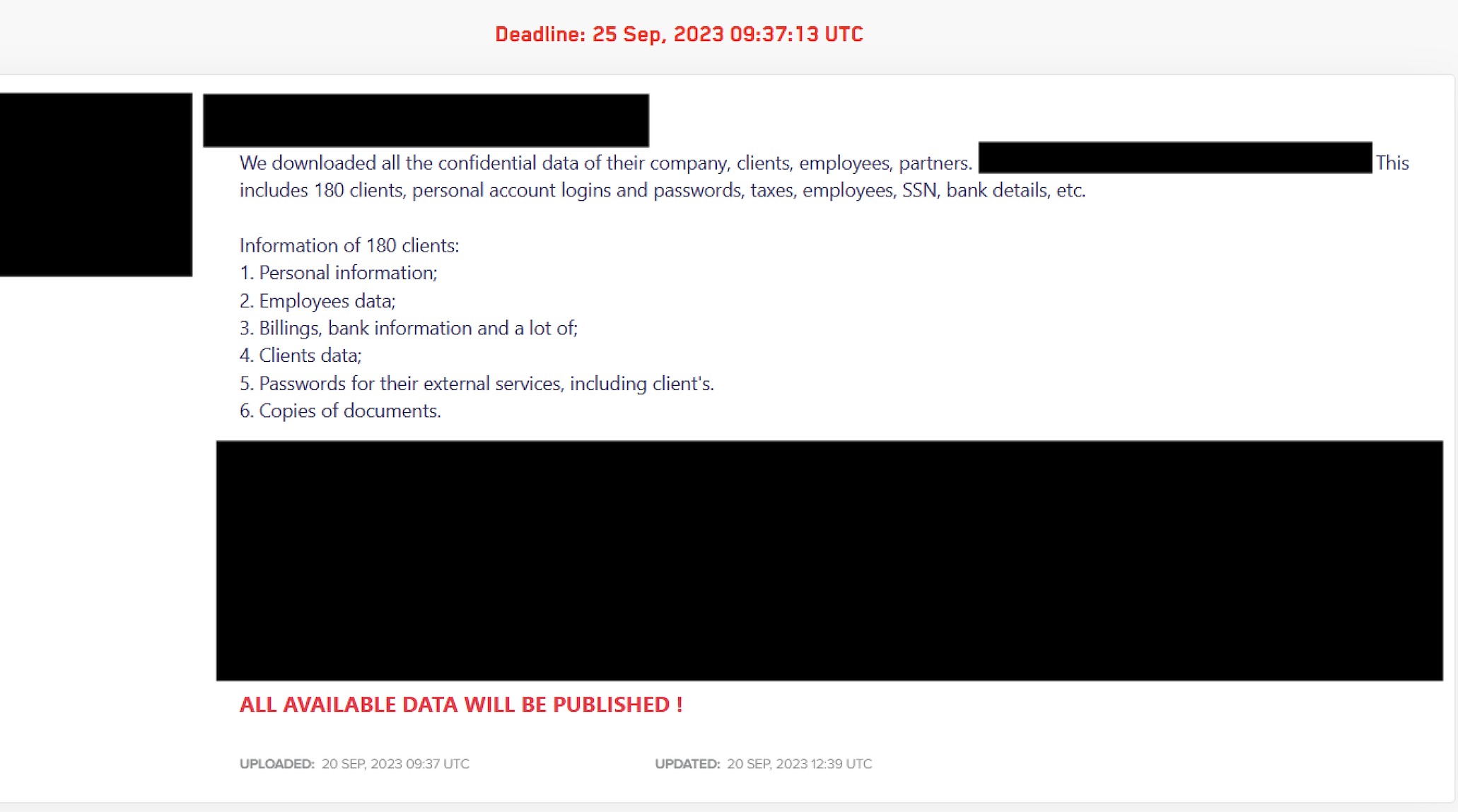
The announcement was posted to LockBit’s data leak site. The ransomware group claims they have acquired the confidential data of 180 of the company’s customers.
The group currently has set a deadline for September 25th before they will, they claim, publish all of the data. That if their demands are not met.
A screenshot of the announcement can be seen below. Part of the announcement has been redacted to protect the name of the company as the incident is still ongoing.
Currently, the company’s website is not functioning.
Who is LockBit?
The LockBit ransomware group is arguably the most prolific ransomware gang in operation today. From July 2022 to June 2023, the group accounted for nearly 28% of all known ransomware attacks.
LockBit is a “ransomware-as-a-service” (RaaS) group that has also developed several variants of ransomware products to perform encryption. The group does publish the data of victims who do not pay the ransom on to their hacking website.
The group primarily posts in Russian and English, but according to its website, the group claims to be located in the Netherlands and is not politically motivated. LockBit typically targets small to medium-sized businesses as opposed to larger enterprises.
Stages of a LockBit Attack
The LockBit attack procedure centers around three main steps: Initial access, lateral movement and privilege escalation, and deployment of the ransomware payload.
Initial access
LockBit often leverages social engineering tactics, like phishing, to access user credentials and gain initial entry into an organization’s network.
Among other tactics, they may also conduct brute force attacks to identify user credentials and enter networks using these stolen passwords, or exploit vulnerabilities to gain a foothold within an organization’s network.
Lateral movement and privilege escalation
Once the attackers have gained initial access, they will attempt to expand their reach within the compromised network. Their goal is to locate sensitive data and systems to encrypt, elevate their access rights, and strengthen their control over the affected system, which allows them to move more freely within the network.
The LockBit script will also attempt to deactivate security measures and other infrastructure the organization has put in place to aid attack prevention or recovery, in order to make it more difficult for organizations to recover from an attack without paying the ransom.
Deployment of ransomware payload
After the threat actors have prepped the victim’s network for attack, they will deploy the ransomware to encrypt victims’ files and data and make the ransom demand.
LockBit ransomware stands out for its ability to spread independently; where other ransomware strains require attackers to quietly reside within an organization’s network for an extended period of time to gain access to multiple systems, LockBit enables the attacker to manually target just one system unit, which will infect other accessible units to run the script and encrypt files.
Preventing a LockBit Attack
While ransomware continues to evolve, “basic” cyber defense measures can often be the most impactful. If they aren’t already, prioritize implementing fundamental prevention steps like:
- Patch management
- Network segmentation
- Least privilege access
- Strong password and MFA requirements
- Employee education
- Regular system backups
